Exploitative Deviation: When and How to Leave GTO to Maximize Profit
Clear definition and purpose
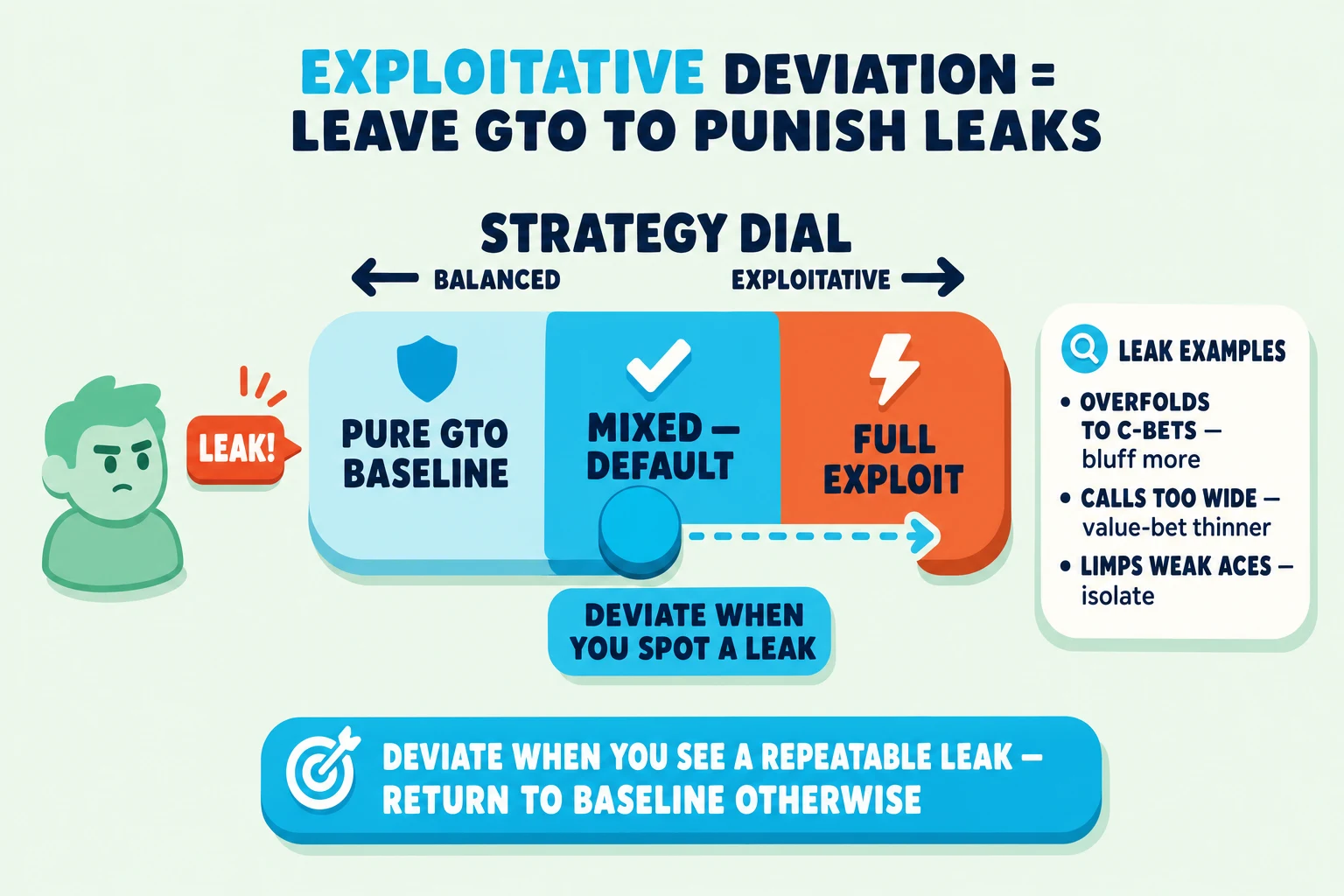
Exploitative deviation means moving away from a balanced GTO (Game Theory Optimal) approach to profit from specific opponents’ mistakes. GTO aims to be unexploitable, but exploitative play deliberately tilts your frequencies and bet choices to punish predictable tendencies. Targets include players who overfold to continuation bets (c-bets - a bet by the preflop aggressor on the flop), opponents who call too wide preflop, or those with predictable post-flop actions. The goal is not a universal strategy but higher expected value (EV) against particular players or tables.
When to deviate exploitatively
Exploitative play is most justified in clear, practical situations:
- Play exploitatively in soft fields and lower-stakes games where many players make consistent, large mistakes.
- Deviate when you spot clear, repeatable leaks, such as opponents folding to specific bet sizes or open-raising very wide.
- Consider table dynamics and image; short sessions, recreational players, or large-field events limit opponent adjustments and favor exploits.
Practical rule: only deviate when you’re confident the opponent’s behavior is stable and profitable to attack.
How to spot opponent leaks quickly
Use focused signals and simple reads to confirm an exploitable tendency:
- Frequency cues. Track concrete stats or behaviors: high fold-to-cbet, low fold-to-3bet, or excessive limping and open-raising.
- Pattern recognition. Notice repeated actions in similar spots - for example, a player who folds the flop after a check, or who calls the flop then folds big turns.
- Tools and observation. Online HUDs (Heads-Up Displays) show frequencies; live reads rely on timing, bet sizing, and showdowns to confirm patterns.
Tip: require multiple instances before committing to a deviation.
Concrete exploitative adjustments to apply
When a leak is confirmed, pick one clear exploit and apply it consistently:
- Increase c-bet/bluff frequency. If an opponent folds too much on certain textures, bluff more on those boards, even with air. Example: You open from the cutoff, miss a K-J-4 rainbow flop, and face a player who folds these flops often - c-bet to take down the pot.
- Widen three-bet or value ranges. Against open-raisers who show many weak hands, three-bet more with value and light hands to isolate and steal pots. Example: Versus a loose early opener, add suited connectors and broadways to your three-bet bluff mix.
- Manipulate sizings. Use smaller bets to induce calls from weak holdings, or larger polarized bets to pressure overcallers who continue with top ranges. Example: Against a calling-station who rarely folds, reduce bluff size to get called; versus a frequent folder, increase sizing to maximize folds.
Managing risks and returning toward balance
Exploitative play carries risk-primarily becoming exploitable yourself if opponents adapt.
- Reassess continuously. Scale back exploitative lines and reintroduce GTO elements when opponents change.
- Mix in balanced lines and vary sizings to avoid easy counter-exploitation when reads are noisy.
- Be selective. Deploy exploitative plays sparingly to limit mental load and avoid overcommitting to fragile reads.
Checklist:
- Confirm a repeatable opponent leak before deviating.
- Choose one clear exploit (c-bet frequency, three-bet width, or sizing) and apply it consistently.
- Monitor for opponent adjustments and revert toward balanced play when uncertainty rises.
- Adjust exploit level to game type (online HUD-enabled games vs live tables) and stakes.